How to hide files in a JPEG image. How to hide files in a JPEG image Hide the exe extension and make it txt
I want to show you one simple and safe way hide files with a simple trick in Windows - hide a file inside a JPG file.
You can actually hide any type of file inside an image file, including TXT, EXE, MP3, AVI, or any other. Not only that, you can store a large number of files inside a single JPG file instead of just one. This can be very convenient when you want to hide files and don't want to bother with ransomware and other file hiding methods.
In order to complete this task, you must have either WinZip or WinRAR installed on your computer.
Here are the steps to create a hidden cache:
Create a folder on your hard drive, for example, C: Test and put all the files you want to hide there. In the same folder, place the image file into which we will “shove” the hidden files.

Now select all the files you want to hide, click right click mouse on them and select the option to add files to the archive. Just select the files you want to hide, not the map file. Name the created archive as you wish, for example - “Hidden.rar”.

Now you have a folder containing JPG file and compressed archive:

Now here's the fun part! Click the Start button and select Run. Type “CMD” without quotes and press Enter. You should now see a window command line. Enter “CD” to get to the root directory. Then enter the command “CD Test” to get into the “Test” folder, which contains all our files.

Now enter next line(without quotes): “ copy /b DSC06578.JPG + Hidden.rar DSC06578.jpg” and press Enter. If everything went well, you should receive a response as shown below:

The JPG file has been updated with a compressed archive inside! Look at the size of the resulting image, you will see that it has increased by the same amount as the archive size.
You can access files hidden inside a picture in two ways.
First, simply change the file extension to .RAR and open the file using WinRAR.
Secondly, you can simply right click on JPG image and select “Open with”, and then select “WinRAR”.

That's it! This is an excellent and simple method simply because not many people know about this possibility and even those who know will not be able to suspect the files in your picture.
And those who don’t can close it right away. 
| Categories: | |
Here is another small program - SteganPEG. It allows you to select any image in the .jpg/.jpeg format and put a certain amount of various files into it, protecting them with a password. The program itself will show you how much volume can fit into a specific image.
In order to get files hidden in the picture you will need the same program and password. The interface, as you can see, is extremely clear:
Added eXe-ImagePacker (600 kb):
Here are some more programs for similar purposes:
Here's some more information
In cheap old spy movies, the most secret documents and unique jewelry were invariably located in a secret safe hidden behind the picture. I don’t know what caused the popularity of this disguise method, but you can do something similar on your computer. Free utility File Camouflage allows you to hide any file, including text, program or other picture, inside any JPG image.

- it's tiny free utility, which allows you to hide confidential information under the guise of harmless images. After downloading and launching the program, we just need to indicate the file that we want to hide, then the picture that will act as a “cover,” and the location where the result will be saved. If desired, you can set a password, without which it will be impossible to extract the file.

To retrieve hidden data, simply switch to the tab De-Camouflage a file, enter the path to the “secret picture” and the save folder. In addition, the program can integrate with Windows Explorer, adding its own item to the “ Send«.
Due to its freeness and ease of use, it may well come in handy in cases where you need to protect your files, but do not want to deal with complex security systems. With this utility, you can quickly and securely hide your data from prying eyes, without raising any unnecessary questions.
Answer
Of course, the program is free and does not require installation. But the archive has a password: http://beloe-bratstvo.ru/
Likewise, you can protect your files with a password, hide them in pictures, and post them publicly.
By the way, the program has one feature: when processing a picture, its original is not saved. That is, you will no longer have this picture without the archive - it will be overwritten. You will not be able to re-use this image to hide another file.
Therefore, it is better to do this: take the ZIP or RAR archive that you want to hide, copy it to the desktop, copy the picture there (only JPG format is suitable) in which you want to hide this archive, and in the program specify the paths to these copies, and not to the originals of the archive and pictures. This is more correct.
Reply With quote To quote bookHello everyone, and today there is a new trick from the Computer76 website, in which I will show you how to hide the file we need in a harmless photo or drawing: how to simply hide a file in a drawing. What kind of file it will be - a harmless joke or - is up to you, but we will try to stuff an executive file with the .exe extension into the drawing. Let's begin.
- First, let's create a new folder. To continue operations, we need to set special parameters for the files being created. To do this, go to the My Computer folder and select Tools – Folder Options…– menu View(in Windows XP).
For Windows 7 the path is: Start - Control Panel - All Control Panel Items (Folder Options). There you will see a window familiar to Windows XP.
So, in order to finally hide the file in the drawing, we need to set the following parameters in the folder properties:
- Activate function Show hidden files and folders
- Deactivate function Hide extensions for registered file types.
In simple terms, we need to see all the files located on the system (including those hidden by this system) and we need the file extension to be displayed in its name. Now you can change not only the name, but also the file extension.
Most important point, which you should not miss: both the Trojan and the shortcut to it must be in the same folder you created!
- Now make a copy of the program (server) and place it in the newly created folder. I suggest renaming it to something harmless. But the victim will not see the .exe extension that we see, unless, of course, he has the same options set. But he will see a completely different file extension. Why? Yes, we'll just replace it. Instead of virus.exe or whatever you have, write something like “I_in_bikini.jpeg”.
Windows will warn you that the file may not be recognized after changing the extension. We ignore it.
- Next, let’s create a shortcut to “I_am_bikini.jpeg” in the same folder. Rename the shortcut to a name, for example, “sunbathing.jpeg”. This is done in order to create the appearance of two different photographs. In my drawing, both photos are named the same. It should look something like this:
Now the basic steps and be careful.
- Let's open the properties of the created shortcut, and in the Shortcut tab enter the following path in the Object field (accordingly, the file name is mine, yours is different):
C:\WINDOWS\system32\cmd.exe /c I'm_in_a_bikini.jpeg
 In the field Working folder The path to the files must be specified. You will have one of your own.
In the field Working folder The path to the files must be specified. You will have one of your own.
The shortcut will have a characteristic icon for belonging to cmd commands; in the figure above it is already visible; we will get rid of it later. As you understand, from this cmd command will launch a disguised Trojan.
Everything is ready, now you can start step by step instructions about how to hide your tracks and confuse the user. First, change the icon of the shortcut, otherwise the console icon betrays us. To do this, in the shortcut properties, return to the tab Label and click on the button Change icon...
 Replace the text in the field with the following path:
Replace the text in the field with the following path:
%SystemRoot%\system32\SHELL32.dll
and choose the one that makes sense. You can look for the shortcut in other folders with other programs.

- Let's hide the Trojan from the user's eyes. Let's go to the tab General and set the option Hidden.
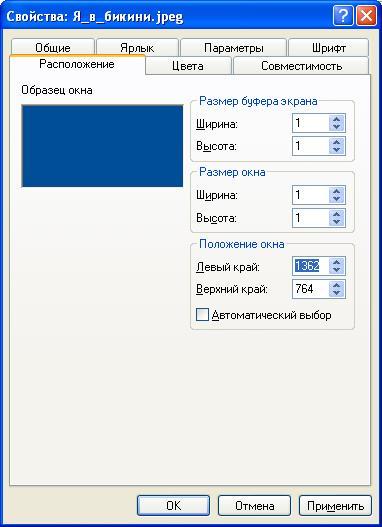
- When run on the victim's computer, the origin of the file will display a command console window that appears. That is, first the famous black console window will appear, and then our program. Let's hide the console, playing on the probability that the user's settings are not maximum resolution on the monitor screen (this is almost always extremely inconvenient and uncomfortable). Let's return to the Trojan shortcut and go to the location tab. Here, set the minimum dimensions of the console window and move it to the right and down as much as possible, unchecking the Automatic selection option. It should look something like this:
Click Apply.
This completes the basic procedures. Now you know how to hide a file in a drawing. Before trying it out, I’ll recommend a few more tips.
- Files should be transferred over the network after they have been packaged in an archive. Not every antivirus will be able to detect the presence of an executable file in the archive. Therefore, use Zip or RAR. Transferring it in an archive as a single file on the network is common and will not cause suspicion.
- You should not send the only “photo” in the archive. This is suspicious. I can suggest that before the attack, make a selection of photographs of a beautiful person, fortunately exposing herself as a fool in social networks complete. And attach your program to the resulting portfolio. Options for luring double click By the required file– sea.
Read: 124
The article shows how you can outwit an attentive user who is familiar with the basics of social engineering, who even monitors file extensions and in no way calls for the use of this information for illegal purposes. The goal is to run an executable file by passing it off as text document in a zip archive, and if it’s unlikely to run, then it won’t allow you to unpack or hide the file.
There is already an article on Habré about the possibility of changing the reading order of Unicode characters using the RLO byte. It says that using standard Windows Explorer, it is difficult to notice the substitution (spoofing) of a file name. It talks about hiding the real file extension. There is also an article about the features of the archiver built into Explorer.
As a person who always monitors the extensions of files that are opened, I was wondering if there are programs that warn about this? In particular, are archivers secure? And what can attackers do to bypass the protection.
As a test subject, let’s take an executable file with the .exe extension, let’s call it “About success” txt.exe».
After the letter "p" in the file name editing mode in context menu Explorer, select “Insert Unicode control character” and select RLO. This will change the file's display name to "About uspexe.txt".
7-Zip 9.20/15.06

WinRAR 5.3

Built into Windows Explorer
As you can see, 7-zip immediately gave up, WinRAR showed an arrow, and the archiver built into Explorer does not support RLO. Now we are thinking, is it possible to somehow perform spoofing with the last two archivers? To do this, open the zipped file in a HEX editor, while simultaneously reading the ZIP format specification.
When compressing a file in zip, the file name is duplicated 2 times.


And here there is a large field for creativity.
Firstly, you can erase the characters of the RLO byte in the second occurrence. WinRAR will then display the file name “About uspexe.txt” and open it as a text document. However, if you go further and change the extension .txt to .jpg, then up to version WinRAR 4.20 this pseudo-image will be launched as an application. This vulnerability no longer exists in WinRAR 5.3b2.
Having opened a file with the RLO erased in the second occurrence in the archiver built into Windows Explorer, you can observe that the file name has become almost readable - only Russian letters are unreadable. To make the name readable, we will replace their encoding or write Latin ones. However, we don't want the user to open the program as a text document.
To stop Explorer's archiver from seeing a file, just specify one of the reserved ones in the file name. file system NTFS characters (for example,<). Однако, это не спасет от просмотра архива WinRAR-ом. Что же делать? Добавить null-байт в начало имени файла!

Then a small miracle will happen: WinRAR 5.3b will display the file as the “Local Disk” folder, by going to which inside the archiver, WinRAR will automatically unpack our file with the RLO symbol in the name (the name for unpacking is taken from the first occurrence!) into the “Temp\ Rar$” directory *" and carefully displays the executable file in Explorer as a text document! Please note that after closing the archiver will carefully try to delete this file like any other file unpacked into a temporary directory.

You can simultaneously make it so that it can be read by the Explorer archiver. Then instead of null you need to enter another non-printable character.
Resume
- 7-Zip 15.06 displays the filename from the first occurrence (with the RLO character). The executable file is presented as a text document. Even if you have enabled displaying extensions of registered file types. Double-clicking in the archiver window will launch the executable file.
- The internal Windows archiver does not see this particular file. Sees other files.
- WinRAR 5.3b displays the file as a “Local Disk” folder, by going to which inside the archiver, WinRAR automatically unpacks our file with a substitute name (with an RLO symbol) - the name for unpacking is taken from the first occurrence - into the “Temp” directory and carefully shows it in Explorer executable file as a text document!
But not everything is so sad. 7-Zip, for example, up to version 9.20 displays the file name from the second occurrence. However, if you do not change the file name in the second entry and make not a Zip archive, but some rare one, of these three archivers, only 7-Zip can be opened, and put it in our Zip archive (do not find a familiar template - release of a broken program , where usually a bunch of archives with readme.txt files are placed?), then the attack will work on it too. Moreover, version 9.20 also incorrectly displays the name of a file starting with null and will not allow it to be read or unpacked.
Also, the review does not include the WinZip archiver. To be honest, I didn't like it because of the size, appearance and advertising in the unregistered version. However, in terms of warning the user about executable files and files with incorrect names, it passed all tests.
The file sample.zip is an example of creating such an archive. Inside is a program with a notepad icon that launches notepad. Doesn't do anything else. Hides from the archiver built into Explorer, forces WinRAR 5.3 to be automatically unpacked, displays the .txt extension in 7-zip version 15
Another example is Sample 2 for all versions of 7-zip, WinRAR 3.8, Windows Explorer. Everywhere there is a file with the extension *.txt
The article shows how you can outwit an attentive user who is familiar with the basics of social engineering, who even monitors file extensions and in no way calls for the use of this information for illegal purposes. The goal is to launch an executable file, passing it off as a text document in a zip archive, and if it is unlikely to run, then prevent the file from being unpacked or hidden.
There is already an article on Habré about the possibility of changing the reading order of Unicode characters using the RLO byte. It says that using standard Windows Explorer, it is difficult to notice the substitution (spoofing) of a file name. It talks about hiding the real file extension. There is also an article about the features of the archiver built into Explorer.
As a person who always monitors the extensions of files that are opened, I was wondering if there are programs that warn about this? In particular, are archivers secure? And what can attackers do to bypass the protection.
As a test subject, let’s take an executable file with the .exe extension, let’s call it “About success” txt.exe».
After the letter “p”, in the file name editing mode, in the Explorer context menu, select “Insert Unicode control character” and select RLO. This will change the file's display name to "About uspexe.txt".
Spoiler: 1
7-Zip 9.20/15.06
Spoiler: 2

Spoiler: 3

Built into Windows Explorer
As you can see, 7-zip immediately gave up, WinRAR showed an arrow, and the archiver built into Explorer does not support RLO. Now we are thinking, is it possible to somehow perform spoofing with the last two archivers? To do this, open the zipped file in a HEX editor, while simultaneously reading the ZIP format specification.
When compressing a file in zip, the file name is duplicated 2 times.
Spoiler: First occurrence

Spoiler: Second occurrence

And here there is a large field for creativity.
Firstly, you can erase the characters of the RLO byte in the second occurrence. WinRAR will then display the file name “About uspexe.txt” and open it as a text document. However, if you go further and change the extension .txt to .jpg, then up to version WinRAR 4.20 this pseudo-image will be launched as an application. This vulnerability no longer exists in WinRAR 5.3b2.
Having opened a file with the RLO erased in the second occurrence in the archiver built into Windows Explorer, you can observe that the file name has become almost readable - only Russian letters are unreadable. To make the name readable, we will replace their encoding or write Latin ones. However, we don't want the user to open the program as a text document.
To stop Explorer's archiver from seeing a file, just specify one of the reserved filenames in the file name. NTFS system characters (for example,<). Однако, это не спасет от просмотра архива WinRAR-ом. Что же делать? Добавить null-байт в начало имени файла!

Then a small miracle will happen: WinRAR 5.3b will display the file as the “Local Disk” folder, by going to which inside the archiver, WinRAR will automatically unpack our file with the RLO symbol in the name (the name for unpacking is taken from the first occurrence!) into the “Temp\ Rar$” directory *" and carefully displays the executable file in Explorer as a text document! Please note that after closing the archiver will carefully try to delete this file like any other file unpacked into a temporary directory.

You can simultaneously make it so that it can be read by the Explorer archiver. Then instead of null you need to enter another non-printable character.
Resume
- 7-Zip 15.06 displays the filename from the first occurrence (with the RLO character). The executable file is presented as a text document. Even if you have enabled displaying extensions of registered file types. Double-clicking in the archiver window will launch the executable file.
- The internal Windows archiver does not see this particular file. Sees other files.
- WinRAR 5.3b displays the file as the “Local Disk” folder, by going to which inside the archiver, WinRAR automatically unpacks our file with a substitute name (with the RLO symbol) - the name for unpacking is taken from the first occurrence - into the “Temp” directory and carefully shows it in Explorer executable file as a text document!










